I enjoy hacking, although I’ve not always referred to it as such. Back in the day, I called it snooping, and it helped out tremendously when writing some of my early books and magazine articles.
I did my best snooping by using a debugger. I would load a program’s code into the debugger, not to see how they wrote the code, but to look for secrets.
For example, upon debugging the DOS command processor, I would discover hidden and secret switches for the various commands. They would be listed along with the documented options, only they weren’t documented. So I’d try them out and see what they did.
This type of snooping was done well before the Internet. So I couldn’t just find an undocumented switch and look it up on the Internet. Occasionally, when I had contact with Microsoft, I was able to get an answer as to the reason why something was undocumented or what the switch really did. Honestly, I never found the “Go Faster” option on anything. Most of the secrets were simply options used by the programmers to debug or test.
My snooping continued and I made some interesting discoveries. Call it hacking if you will, but such persistence does pay off. Recently, I applied these techniques to the Chrome web browser.
Chrome doesn’t really use dialog boxes. Instead, its settings and options are displayed in a web browser window. You just need to type the “address” of the item you want and Chrome displays the information like a web page.
For example, Chrome settings are made by typing the address chrome://settings.
Review your bookmarks by typing chrome://bookmarks
And that’s where my snooping gene activated. As you type chrome:// and then another letter, the AutoComplete function offers suggestions. That’s how you can see the pantheon of Chrome options and settings, including some that may not be accessed in other ways or could even be undocumented.
For example, type chrome://b and you see a list similar to Figure 1.
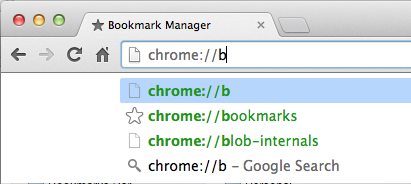
Figure 1. Discover Chrome internals, thanks to AutoComplete.
What are blob-internals? Sounds medical. Anyway, choose that option and you see a confusing list of whatever, which could be interesting, useful, or trivial — take your pick.
So I went on a hunt. I typed chrome://a through chrome://z to see what came up. And for many letters of the alphabet, AutoComplete supplied me with a list of Chrome options and settings. I tried a few of them, and honestly, the majority are truly trivial.
Still, that’s the kind of snooping I do, or call it hacking if you will. It’s not illegal and I’m not spreading viruses or anything that Google doesn’t want you to know about. It’s just a fun way for me to pass the time and maybe discover an actual secret. That’s how it works.


Im curious which debugger you use? Most debuggers programmers use are overly simplistic and just step through a program and display the current values in variables. The debuggers hackers use are debugger/disassembler like IDA and Ollydbg which allow you to see all the machine code in a program. If professional programmers learned how to use these kind of debuggers then they could prevent hackers from most of their exploits.
Comment by BradC — July 10, 2015 @ 12:48 pm
I use only simple debuggers, but I’ll check out those you mention. I miss my powerful debugger, Commander 80, which I used on the TRS-80 to learn about Assembly language and machine code.
Comment by admin — July 10, 2015 @ 2:39 pm
Id like to suggest that as a book topic. All the books on white hat hacking a super difficult to understand and written only for experienced reverse engineering programmers. If you were to write a book like “Ollydbg for Dummies”, that could be a huge hit as it would open up an area of debugging sophistication that has never been taught in layman terms.
Comment by BradC — July 10, 2015 @ 4:01 pm
That book would be a tough sell, more so because it’s highly likely the book would be illegally downloaded more than it would be sold.
I do, however, appreciate your confidence in my ability to write such a book! 😀
Comment by admin — July 10, 2015 @ 4:11 pm